commit a461fd70445aec9dfa34bf9c5a29a85e0ad0e2fe Author: Adolf Belka <adolf.belka@ipfire.org> Date: Sat May 10 12:30:56 2025 +0200 chpasswd.cgi: Fixes bug12755 - v3 with password verification correction - v3 version based on feedback from @Michael to use the status value returned from using the htpasswd command. - Also simplified the whole section to carry out the change if the status is 0, ie all went well, otherwise give an error but without identifying if the error is in the username or the password. This makes it more secure as any attacker only knows it failed and doesn't know if any part of the authentication was correct or not. - Changed the error messages in line with this so the language file changes are in the other part of this patch set submission. - Tested out on my vm test bed and worked fine. If the username was incorrect or the password was incorrect or both were incorrect the same error message is given. If both are correct then the update is carried out. Fixes: bug12755 Tested-by: Adolf Belka <adolf.belka@ipfire.org> Signed-off-by: Adolf Belka <adolf.belka@ipfire.org> Signed-off-by: Michael Tremer <michael.tremer@ipfire.org> commit 9c0dab3d3ca807e836823253aced80a14bc1970a Author: Michael Tremer <michael.tremer@ipfire.org> Date: Wed May 7 09:06:12 2025 +0000 chpasswd.cgi: Add missing $ Signed-off-by: Michael Tremer <michael.tremer@ipfire.org> commit 4c39e38f90fea60ef62e07267fd84f1b89de0297 Author: Adolf Belka <adolf.belka@ipfire.org> Date: Tue May 6 16:10:11 2025 +0200 chpasswd.cgi: Make swroot refs the same as for other cgi files - This uses the swroot definition from general-functions.pl and makes the definition the same as used in the majority of other IPFire cgi files. Tested-by: Adolf Belka <adolf.belka@ipfire.org> Signed-off-by: Adolf Belka <adolf.belka@ipfire.org> Signed-off-by: Michael Tremer <michael.tremer@ipfire.org> commit 6c1549ff7a9c8e3f9f17a29a6b169fce175fea42 Author: Adolf Belka <adolf.belka@ipfire.org> Date: Tue May 6 16:10:09 2025 +0200 chpasswd.cgi: Fixes bug12755 - proxy auth password problem longer than 8 chars - The existing version of the perl module Apache::Htpasswd was using the crypt hash for the password hashing, which is very insecure. The only alternative with this module is the md5 and sha1 hashes which are also considered weak now. - The module was last updated in Nov 2012 and there is no alternative module available. - This patch replaces that perl module with using the apache htpasswd program. This can be set to use the bcrypt hash which is considered secure. This is used for the generation of the root and admin passwords during the IPFire install. - Tested out on my vm testbed system and the password for a specific user name was changed successfully without any restriction to the length of the password. - Existing passwords with the existing md5 or crypt options will still work as htpasswd can manage different encoding hashes in the one file. Fixes: bug12755 Tested-by: Adolf Belka <adolf.belka@ipfire.org> Signed-off-by: Adolf Belka <adolf.belka@ipfire.org> Signed-off-by: Michael Tremer <michael.tremer@ipfire.org> Signed-off-by: Vincent Li <vincent.mc.li@gmail.com>
BPFire - eBPF Network Firewall OS (eBPF 网络防火墙)
What is BPFire?
BPFire is fork of IPFire 2.x, a hardened, versatile, state-of-the-art Open Source firewall based on Linux. BPFire is to enable revolutionary eBPF technology for non-tech savvy users, make eBPF technology consumable to home users or any size of organizations to secure their network environment. Current supported eBPF network application features:
BPFire 基于IPFire 2.x, 一个基于Linux的安全坚固、多功能、先进的开源防火墙. BPFire 为普罗大众带来革命创新性的eBPF技术,为家庭用户或任何大小组织企业的网络安全保驾护航. 当前支持的eBPF应用包括:
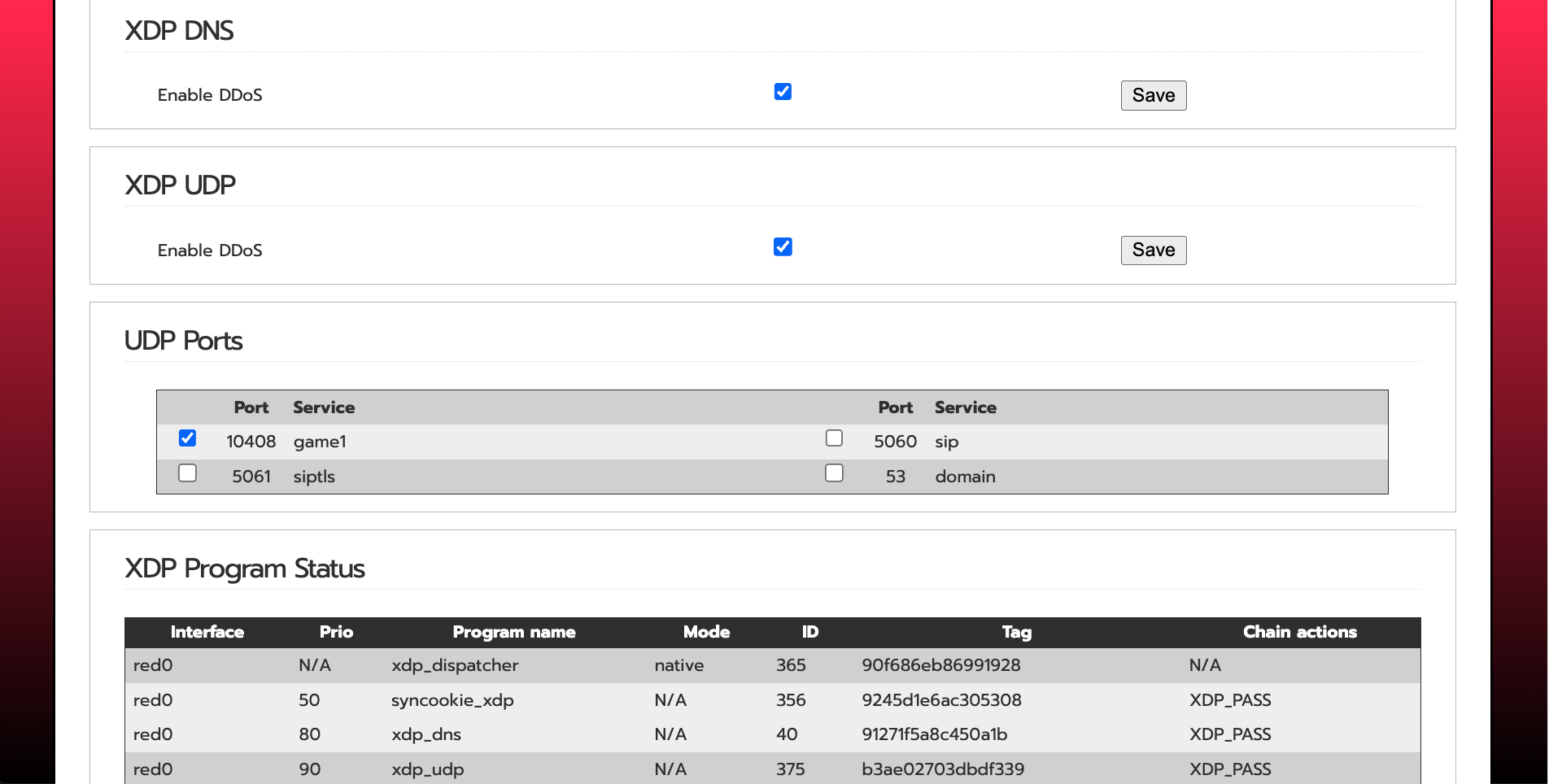
- XDP DDoS protection, See XDP SYNPROXY stops 10G DDoS SYN flood here
- XDP UDP DDoS online game protection
- XDP DNS domain blocklist, ratelimit protection
- XDP SSL/TLS server name indicator (SNI) blocklist
- XDP GeoIP/Country blocklist
- XDP multi attachment and capture mode for Intrusion Detection System Suricata in IPS mode
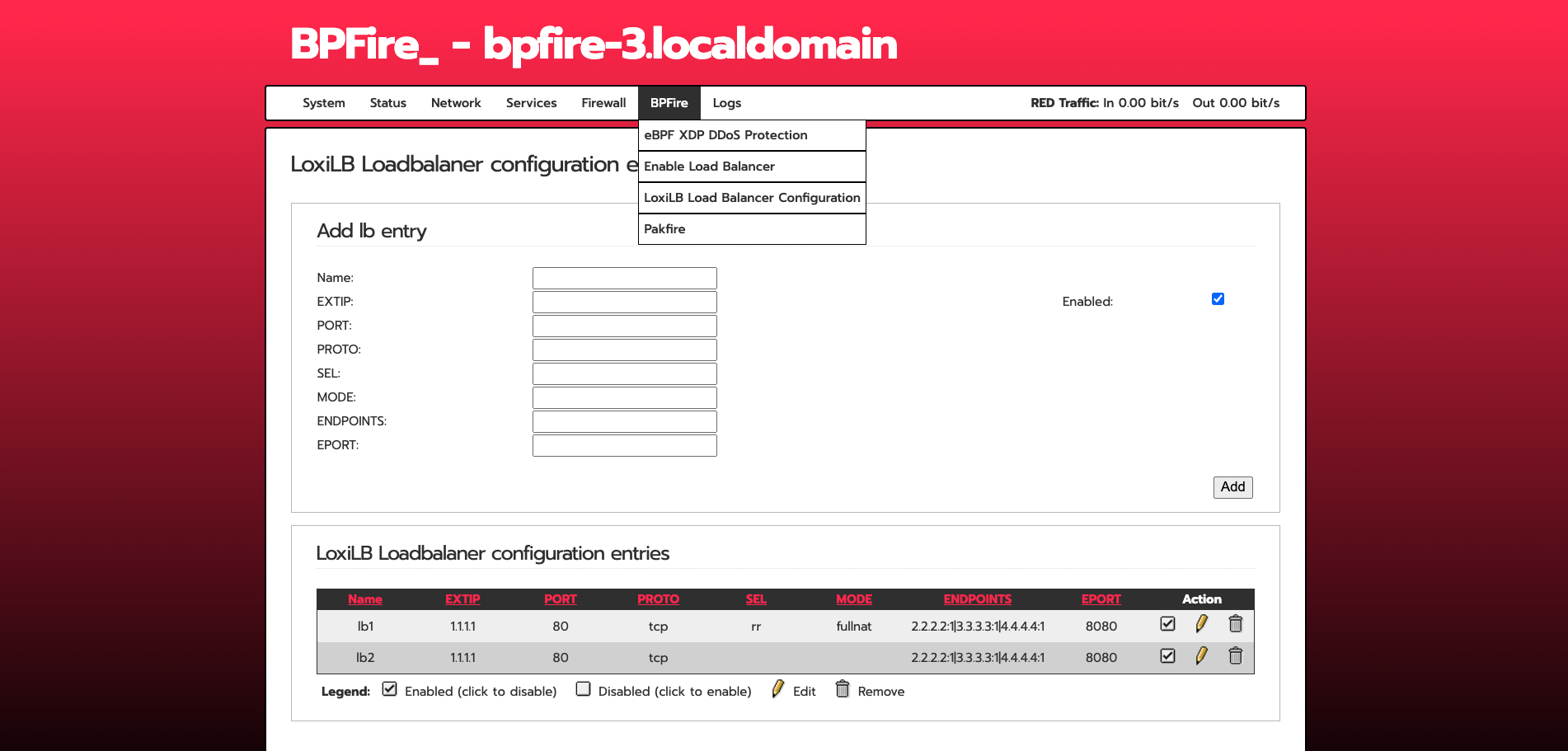
- eBPF based LoxiLB load balancer, Firewall, Proxy, see full features LoxiLB
Where can I get support?
Open github issue or discord
Where can I get BPFire installation ISO or LoongFire flash image?
中国大陆用户下载地址:
Other download site:
What computer hardwares BPFire support?
BPFire support commodity computer hardware, small or large, old or new, cheap or expensive.
for example:
How do I install BPFire?
flash the ISO to USB on Linux machine, /dev/sdc is your USB thrumb drive.
dd if=bpfire-2.29-core184-x86_64.iso of=/dev/sdc status=progress
BPFire installation on mini industrial PC:
BPFire SYNPROXY throughput with and without XDP acceleration under 10Gbit DDoS SYN flood:
BPFire WebUI screenshot:
English:
Chinese:
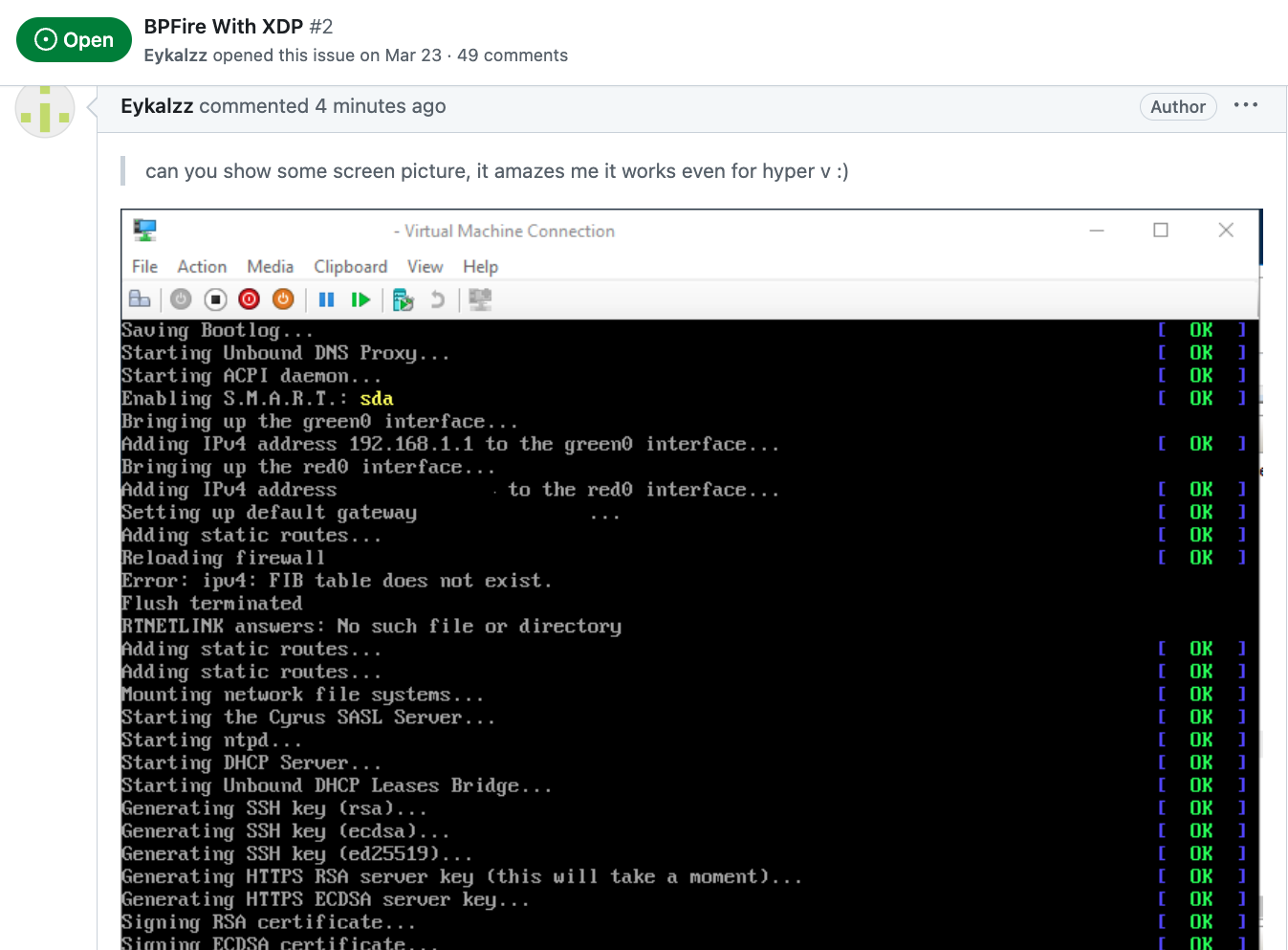
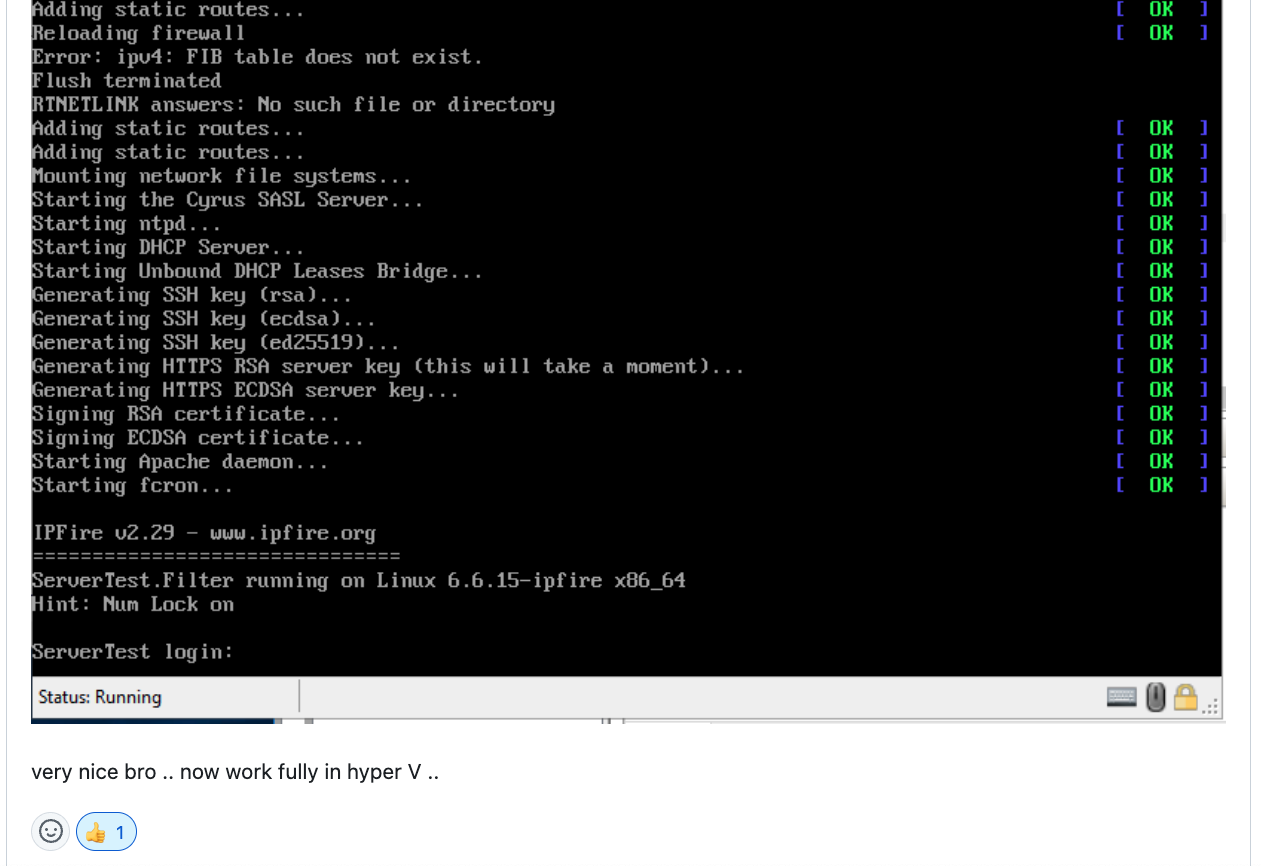
Does BPFire run in hypervisor virtual environment?
Yes, We have tested in Linux KVM hypervisor, Proxmox, Microsoft Hyper-v, should support Virtualbox, VMware as well.
Microsoft Hyper-v screen shot:
How to build BPFire?
Build Environment Setup https://www.ipfire.org/docs/devel/ipfire-2-x/build-initial
(It takes a few hours to build image for first build depending on build machine power)
for example on Ubuntu 22.04 LTS:
apt install git-core g++ manpages-pl patch byacc make autoconf automake libltdl-dev
git clone https://github.com/vincentmli/bpfire.git
cd bpfire
wget --mirror --convert-links --adjust-extension --page-requisites --no-parent --cut-dirs=2 -nH --reject "index.html*" --reject "*.gif" https://www.bpfire.net/download/bpfire/cache/
./make.sh build
How do I support BPFire development?
Join or Donate to BPFire paypal