commit f0812939ca4f6332d34715673c4fe44fbb1a491b (HEAD -> main, origin/main, origin/HEAD)
Author: Vincent Li <vincent.mc.li@gmail.com>
Date: Mon Nov 3 21:46:30 2025 -0800
tc-basic-classifier: add IFB setup in user space
Add the required kernel modules setup and green0 ingress mirror to ifb0
egress setup in class_filter so it is easier for user. see [0] for
required kernel modules and ingress shaping. also change the default
path to /usr/lib/bpf/class_filter.bpf.o also change the default bpf
object path to /usr/lib/bpf/class_filter.bpf.o.
[0]: https://std.rocks/gnulinux_network_traffic_control.html
for example:
Complete setup with one command (IFB mirroring + BPF attachment)
./class_filter -i green0 -3 10mbit -I -a -v
Setting up IFB mirroring for ingress traffic shaping on green0
Loading required kernel modules...
Executing: modprobe ifb numifbs=1
Loaded module: ifb numifbs=1
Executing: modprobe sch_fq_codel
Loaded module: sch_fq_codel
Executing: modprobe act_mirred
Loaded module: act_mirred
Executing: modprobe act_connmark
Loaded module: act_connmark
Successfully loaded all required kernel modules
Executing: ip link set dev ifb0 up
Executing: tc qdisc del dev green0 ingress 2>/dev/null
Executing: tc qdisc add dev green0 ingress handle ffff:
Executing: tc filter add dev green0 parent ffff: protocol ip u32 match u32 0 0 action connmark action mirred egress redirect dev ifb0 flowid ffff:1
Successfully setup IFB mirroring:
- Ingress traffic from green0 mirrored to ifb0 egress
Verification - IFB status:
Executing: ip link show ifb0
7: ifb0: <BROADCAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc htb state UNKNOWN mode DEFAULT group default qlen 32
link/ether 8e:52:c9:93:13:34 brd ff:ff:ff:ff:ff:ff
TC configuration on green0 ingress:
Executing: tc qdisc show dev green0
qdisc fq_codel 8001: root refcnt 9 limit 10240p flows 1024 quantum 1514 target 5ms interval 100ms memory_limit 32Mb ecn drop_batch 64
qdisc ingress ffff: parent ffff:fff1 ----------------
Executing: tc filter show dev green0 parent ffff:
filter protocol ip pref 49152 u32 chain 0
filter protocol ip pref 49152 u32 chain 0 fh 800: ht divisor 1
filter protocol ip pref 49152 u32 chain 0 fh 800::800 order 2048 key ht 800 bkt 0 flowid ffff:1 not_in_hw
match 00000000/00000000 at 0
action order 1: connmark zone 0 pipe
index 1 ref 1 bind 1
action order 2: mirred (Egress Redirect to device ifb0) stolen
index 1 ref 1 bind 1
Setting up TC qdisc and classes on ifb0 for egress shaping...
Executing: tc qdisc del dev ifb0 root 2>/dev/null
Executing: tc qdisc add dev ifb0 root handle 1:0 htb default 30
Executing: tc class add dev ifb0 parent 1:0 classid 1:1 htb rate 100mbit
Warning: sch_htb: quantum of class 10001 is big. Consider r2q change.
Executing: tc class add dev ifb0 parent 1:1 classid 1:30 htb rate 5mbit ceil 10mbit
Successfully setup TC qdisc and classes on ifb0
TC configuration on ifb0:
Executing: tc qdisc show dev ifb0
qdisc htb 1: root refcnt 2 r2q 10 default 0x30 direct_packets_stat 1 direct_qlen 32
Executing: tc class show dev ifb0
class htb 1:1 root rate 100Mbit ceil 100Mbit burst 1600b cburst 1600b
class htb 1:30 parent 1:1 prio 0 rate 5Mbit ceil 10Mbit burst 1600b cburst 1600b
Automatically attaching BPF program to ifb0 for classification...
Attaching BPF program to ifb0...
Executing: tc filter del dev ifb0 protocol ip parent 1:0 2>/dev/null
Command failed but ignoring (may be normal): tc filter del dev ifb0 protocol ip parent 1:0 2>/dev/null
Executing: tc filter add dev ifb0 protocol ip parent 1:0 bpf obj ./class_filter.bpf.o classid 1: direct-action
Successfully attached BPF program to ifb0 egress (parent 1:0)
BPF maps automatically pinned to /sys/fs/bpf/tc/globals/
Verification:
Executing: tc filter show dev ifb0 parent 1:0
filter protocol ip pref 49152 bpf chain 0
filter protocol ip pref 49152 bpf chain 0 handle 0x1 flowid 1: class_filter.bpf.o:[classifier] direct-action not_in_hw id 100 name cls_filter tag 7163f8c072cf7015 jited
Pinned maps:
Executing: ls -la /sys/fs/bpf/tc/globals/ 2>/dev/null || echo 'No pinned maps found'
total 0
drwx------ 2 root root 0 Nov 3 11:43 .
drwx------ 3 root root 0 Nov 3 11:24 ..
-rw------- 1 root root 0 Nov 3 11:43 cls_filter_ip_trie_map
-rw------- 1 root root 0 Nov 3 11:43 cls_filter_port_map
Complete setup finished:
- IFB mirroring configured on green0 -> ifb0
- TC qdisc and classes setup on ifb0
- BPF classifier attached to ifb0 egress
- Ready for port/IP based traffic classification!
Signed-off-by: Vincent Li <vincent.mc.li@gmail.com>
Signed-off-by: Vincent Li <vincent.mc.li@gmail.com>
BPFire - eBPF Network Firewall OS (eBPF 网络防火墙)
What is BPFire?
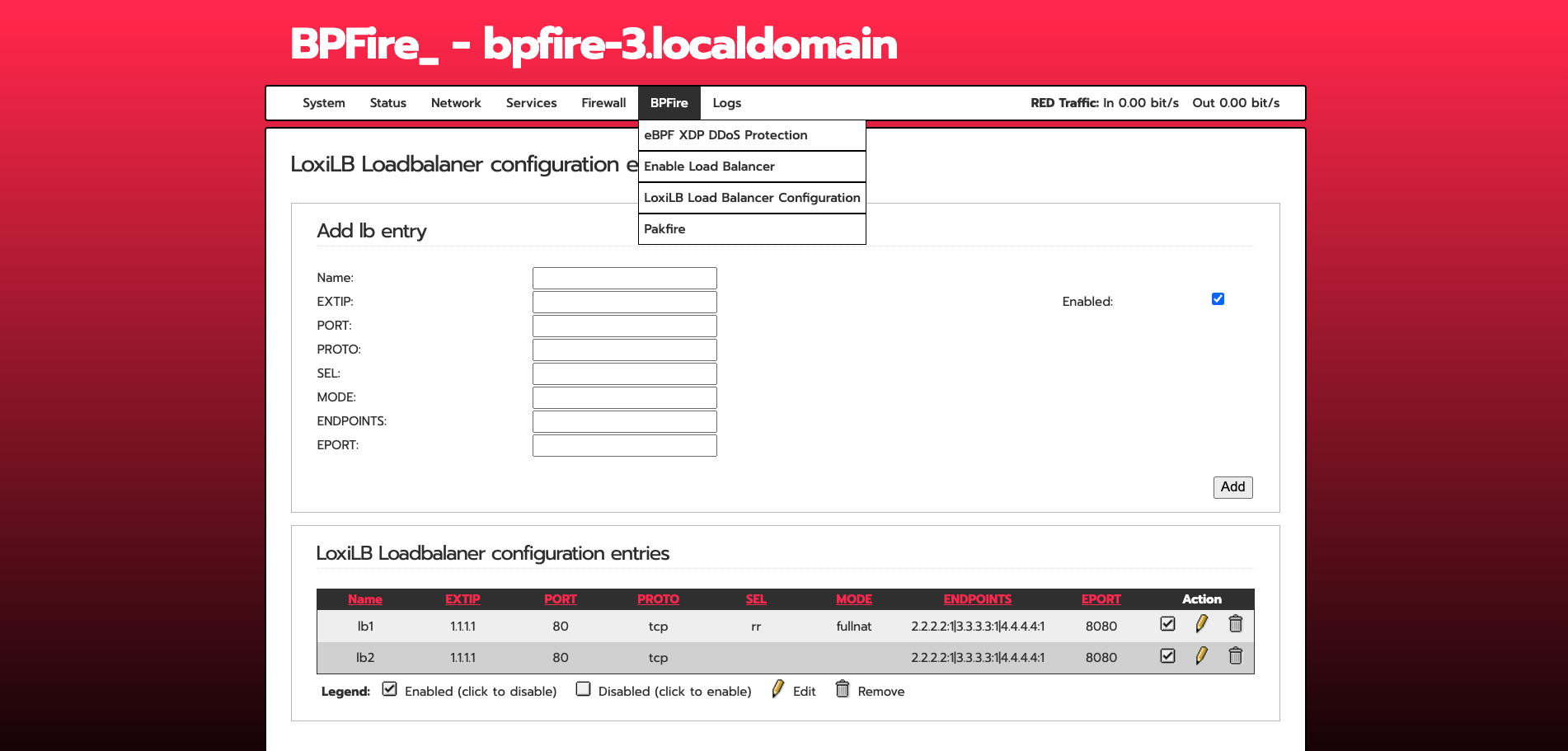
BPFire is fork of IPFire 2.x, a hardened, versatile, state-of-the-art Open Source firewall based on Linux. BPFire is to enable revolutionary eBPF technology for non-tech savvy users, make eBPF technology consumable to home users or any size of organizations to secure their network environment. Current supported eBPF network application features:
BPFire 基于IPFire 2.x, 一个基于Linux的安全坚固、多功能、先进的开源防火墙. BPFire 为普罗大众带来革命创新性的eBPF技术,为家庭用户或任何大小组织企业的网络安全保驾护航. 当前支持的eBPF应用包括:
- XDP DDoS protection, See XDP SYNPROXY stops 10G DDoS SYN flood here
- XDP UDP DDoS online game protection
- XDP DNS domain blocklist, ratelimit protection
- XDP SSL/TLS server name indicator (SNI) blocklist
- XDP GeoIP/Country blocklist
- XDP multi attachment and capture mode for Intrusion Detection System Suricata in IPS mode
- eBPF based LoxiLB load balancer, Firewall, Proxy, see full features LoxiLB
Where can I get support?
Open github issue or discord
Where can I get BPFire installation ISO or LoongFire flash image?
中国大陆用户下载地址:
Other download site:
What computer hardwares BPFire support?
BPFire support commodity computer hardware, small or large, old or new, cheap or expensive.
for example:
How do I install BPFire?
flash the ISO to USB on Linux machine, /dev/sdc is your USB thrumb drive.
dd if=bpfire-2.29-core184-x86_64.iso of=/dev/sdc status=progress
BPFire installation on mini industrial PC:
BPFire SYNPROXY throughput with and without XDP acceleration under 10Gbit DDoS SYN flood:
BPFire WebUI screenshot:
English:
Chinese:
Does BPFire run in hypervisor virtual environment?
Yes, We have tested in Linux KVM hypervisor, Proxmox, Microsoft Hyper-v, should support Virtualbox, VMware as well.
Microsoft Hyper-v screen shot:
How to build BPFire?
Build Environment Setup https://www.ipfire.org/docs/devel/ipfire-2-x/build-initial
(It takes a few hours to build image for first build depending on build machine power)
for example on Ubuntu 22.04 LTS:
apt install git-core g++ manpages-pl patch byacc make autoconf automake libltdl-dev
git clone https://github.com/vincentmli/bpfire.git
cd bpfire
wget --mirror --convert-links --adjust-extension --page-requisites --no-parent --cut-dirs=2 -nH --reject "index.html*" --reject "*.gif" https://www.bpfire.net/download/bpfire/cache/
./make.sh build
How do I support BPFire development?
Join or Donate to BPFire paypal